
We always upgrade our products with latest 300-715 exam questions for Cisco exam. By using the 300-715 braindumps from Soaoj, you will be able to pass Cisco 300-715 Exam in the first attempt. You can always try our free 300-715 demo before spending your money on Cisco exam dumps.
Cisco 300-715 Fragen&Antworten Sie sind außerdem billig, Cisco 300-715 Fragen&Antworten Kann ich PDF-Dateien erwerben, Cisco 300-715 Fragen&Antworten Wir haben die neuesten und genauesten Schulungsunterlagen, die Sie brauchen, Cisco 300-715 Fragen&Antworten PDF ist sozusagen die klassischste und üblichste Version, denn man kann sie als Lehrbuch drucken und dann die Übungen darauf schreiben, Beeilen Sie sich Soaoj 300-715 Prüfungsfrage in Ihren Einkaufswagen hinzuzufügen.
Moment mal fuhr ich dazwischen, Für diesen Pastor, wenn wir bei dieser Bezeichnung 300-715 PDF Testsoftware bleiben wollen, gibt es keine Garantien, Der Begriff ist Riff über die Verwendung von Statistiken im Baseball, die Sabermetrics genannt wird.
Arya rannte zum Pier, Und Rosalie glaubt, bei deinem 300-715 Fragen&Antworten Temperament hat Jasper die besseren Karten, Du vielleicht auch, Die meisten Forschungsteams sind Wissenschaftler und verarbeiten LinkedIn-Daten 300-715 in der Hoffnung, neue Einblicke in die Weltwirtschaft und die Arbeitsmärkte zu erhalten.
Vielleicht sollten wir die Begriffe von Karpie und der Handelsabteilung 300-715 Prüfungen kombinieren, Man findet Social Proof in der Kleidermode, bei Managementtechniken, im Freizeitverhalten, in der Religion und bei Diäten.
Heute bin ich ausgegangen, um zu sehen, ob das Glück mir auch jemanden bescheren 300-715 Fragen&Antworten würde, und es hat mich Dir zugeführt, Aus dem Teig formt man kleine Plaetzchen, die man in dem heiss und still gewordenen Fett in der Pfanne baeckt.
Wabbel kann hineinsteigen Hier, Wabbel, Für die Kunst 300-715 Fragen&Antworten sind die Anforderungen an die Fotografie absolut, Wenn ein Geheimdienst eine verschlüsselteNachricht mit möglicherweise sehr sensiblen Informationen 300-715 Fragen&Antworten abfing, wurde diese Information stückchenweise von mehreren Sachbearbeitern dechiffriert.
Hinter der Tür führte eine Wendeltreppe in den Kerker, Ich C_SACP_2321 Prüfungsfrage hab es überhaupt nicht so gemeint, Gottlob, ihr fällt sonst niemand ein, Dies ist eine sehr schmerzhafte Lektion.
Dort erhielten Tengos Vater und seine Kameraden 300-715 Deutsch ein Stück Ackerland, Gerätschaften und ein kleines Gewehr und sollten nun Landwirtschaft betreiben, Drei Beobachtungen, 300-715 Schulungsunterlagen die ich kürzlich gemacht habe, haben dieses Konzept zu mir nach Hause gebracht.
Er kann keinen Flecken an seinem Herzog dulden, und er hielt Community-Cloud-Consultant Lernressourcen mich für deinen Flecken, Befiel jetzt Deinem Knecht, dass er Deine Pferde, Waffen und Gerätschaften hineinbringe.
Aber es kam nicht zur Penetration, Mir ist das NSE7_OTS-7.2 Zertifizierungsfragen egal, Brief) seinem Herzen Luft macht, welches hier, erfreulicher Weise nur vorübergehend, einen ziemlich hohen Grad von bitterer Gereiztheit 300-715 Fragen&Antworten zeigt, da er wie Faust in seinem dunkeln Drange sich seines rechten Weges wohl bewußt war.
Geduldig wartete ich, bis sie die Lider mit etwas verklebten Wimpern 500-220 Fragen Und Antworten hob, hielt ihr das Tütchen hin, doch sie bemerkte den Waldmeister nicht, schien durch das Tütchen und Oskar hindurchzusehen.
Zu diesem Zeitpunkt unterscheidet er zwischen Patienten und Nichtpatienten, 300-715 Pruefungssimulationen Klepp rieb mich warm, Diese Maßnahmen sind herausragende technische Leistungen, Kann ich ein bisschen bei Ihnen sitzen fragte Fukaeri.
sagte Carlisle vorwurfsvoll, Durch die Integration intelligenter Cloud-Speicher 300-715 Fragen&Antworten für unstrukturierte Dateidaten werden Komplexität und Kosten reduziert und gleichzeitig die Produktivität gesteigert.
NEW QUESTION: 1
This type of attack is generally most applicable to public-key cryptosystems, what type of attack am I ?
A. Plaintext Only Attack
B. Ciphertext-only attack
C. Chosen-Ciphertext attack
D. Adaptive-Chosen-Plaintext attack
Answer: C
Explanation:
Explanation/Reference:
A chosen-ciphertext attack is one in which cryptanalyst may choose a piece of ciphertext and attempt to obtain the corresponding decrypted plaintext. This type of attack is generally most applicable to public-key cryptosystems.
A chosen-ciphertext attack (CCA) is an attack model for cryptanalysis in which the cryptanalyst gathers information, at least in part, by choosing a ciphertext and obtaining its decryption under an unknown key. In the attack, an adversary has a chance to enter one or more known ciphertexts into the system and obtain the resulting plaintexts. From these pieces of information the adversary can attempt to recover the hidden secret key used for decryption.
A number of otherwise secure schemes can be defeated under chosen-ciphertext attack. For example, the El Gamal cryptosystem is semantically secure under chosen-plaintext attack, but this semantic security can be trivially defeated under a chosen-ciphertext attack. Early versions of RSA padding used in the SSL protocol were vulnerable to a sophisticated adaptive chosen-ciphertext attack which revealed SSL session keys. Chosen-ciphertext attacks have implications for some self-synchronizing stream ciphers as well.
Designers of tamper-resistant cryptographic smart cards must be particularly cognizant of these attacks, as these devices may be completely under the control of an adversary, who can issue a large number of chosen-ciphertexts in an attempt to recover the hidden secret key.
According to RSA:
Cryptanalytic attacks are generally classified into six categories that distinguish the kind of information the cryptanalyst has available to mount an attack. The categories of attack are listed here roughly in increasing order of the quality of information available to the cryptanalyst, or, equivalently, in decreasing order of the level of difficulty to the cryptanalyst. The objective of the cryptanalyst in all cases is to be able to decrypt new pieces of ciphertext without additional information. The ideal for a cryptanalyst is to extract the secret key.
A ciphertext-only attack is one in which the cryptanalyst obtains a sample of ciphertext, without the plaintext associated with it. This data is relatively easy to obtain in many scenarios, but a successful ciphertext-only attack is generally difficult, and requires a very large ciphertext sample. Such attack was possible on cipher using Code Book Mode where frequency analysis was being used and even thou only the ciphertext was available, it was still possible to eventually collect enough data and decipher it without having the key.
A known-plaintext attack is one in which the cryptanalyst obtains a sample of ciphertext and the corresponding plaintext as well. The known-plaintext attack (KPA) or crib is an attack model for cryptanalysis where the attacker has samples of both the plaintext and its encrypted version (ciphertext), and is at liberty to make use of them to reveal further secret information such as secret keys and code books.
A chosen-plaintext attack is one in which the cryptanalyst is able to choose a quantity of plaintext and then obtain the corresponding encrypted ciphertext. A chosen-plaintext attack (CPA) is an attack model for cryptanalysis which presumes that the attacker has the capability to choose arbitrary plaintexts to be encrypted and obtain the corresponding ciphertexts. The goal of the attack is to gain some further information which reduces the security of the encryption scheme. In the worst case, a chosen-plaintext attack could reveal the scheme's secret key.
This appears, at first glance, to be an unrealistic model; it would certainly be unlikely that an attacker could persuade a human cryptographer to encrypt large amounts of plaintexts of the attacker's choosing. Modern cryptography, on the other hand, is implemented in software or hardware and is used for a diverse range of applications; for many cases, a chosen-plaintext attack is often very feasible. Chosen-plaintext attacks become extremely important in the context of public key cryptography, where the encryption key is public and attackers can encrypt any plaintext they choose.
Any cipher that can prevent chosen-plaintext attacks is then also guaranteed to be secure against known- plaintext and ciphertext-only attacks; this is a conservative approach to security.
Two forms of chosen-plaintext attack can be distinguished:
Batch chosen-plaintext attack, where the cryptanalyst chooses all plaintexts before any of them are encrypted. This is often the meaning of an unqualified use of "chosen-plaintext attack".
Adaptive chosen-plaintext attack, is a special case of chosen-plaintext attack in which the cryptanalyst is able to choose plaintext samples dynamically, and alter his or her choices based on the results of previous encryptions. The cryptanalyst makes a series of interactive queries, choosing subsequent plaintexts based on the information from the previous encryptions.
Non-randomized (deterministic) public key encryption algorithms are vulnerable to simple "dictionary"-type attacks, where the attacker builds a table of likely messages and their corresponding ciphertexts. To find the decryption of some observed ciphertext, the attacker simply looks the ciphertext up in the table. As a result, public-key definitions of security under chosen-plaintext attack require probabilistic encryption (i.e., randomized encryption). Conventional symmetric ciphers, in which the same key is used to encrypt and decrypt a text, may also be vulnerable to other forms of chosen-plaintext attack, for example, differential cryptanalysis of block ciphers.
An adaptive-chosen-ciphertext is the adaptive version of the above attack. A cryptanalyst can mount an attack of this type in a scenario in which he has free use of a piece of decryption hardware, but is unable to extract the decryption key from it.
An adaptive chosen-ciphertext attack (abbreviated as CCA2) is an interactive form of chosen-ciphertext attack in which an attacker sends a number of ciphertexts to be decrypted, then uses the results of these decryptions to select subsequent ciphertexts. It is to be distinguished from an indifferent chosen-ciphertext attack (CCA1).
The goal of this attack is to gradually reveal information about an encrypted message, or about the decryption key itself. For public-key systems, adaptive-chosen-ciphertexts are generally applicable only when they have the property of ciphertext malleability - that is, a ciphertext can be modified in specific ways that will have a predictable effect on the decryption of that message.
A Plaintext Only Attack is simply a bogus detractor. If you have the plaintext only then there is no need to perform any attack.
References:
RSA Laboratories FAQs about today's cryptography: What are some of the basic types of cryptanalytic attack?
also see:
http://www.giac.org/resources/whitepaper/cryptography/57.php
and
http://en.wikipedia.org/wiki/Chosen-plaintext_attack
NEW QUESTION: 2
Your network contains an Exchange Server 2010 SP1 organization named fabrikam.com.
You have two mailbox-enabled users named user1 and user2.
You need to perform the following tasks:
Ensure that user2 can send email messages as user1.
Ensure that an entry is logged on the server each time user2 sends a message as user1.
review the list of logged email messages.
What should you do? 
A. Create a retention policy.
B. Create a new Hub Transport rule.
C. Modify user1 by using the Set-Mailbox cmdlet.
D. Run a non-owner mailbox access report from the Exchange Control Panel (ECP).
E. Enable a litigation hold for user1.
F. Assign permissions to user1 by using theAdd-ADPermission cmdlet.
G. AssignpermissionstoUser2byusingtheAdd-AdPermissioncmdlet.
H. Modify user2 by using the Set-Mailbox cmdlet.
I. ReviewtheApplicationlogfromtheEventViewer.
Answer: C,D,G
Explanation:
Explanation/Reference:
Order -Assing Permission to user2 > Modify User1 Set-Mailbox > Run non-onwer
NEW QUESTION: 3
展示を参照してください。
tloc-extensionコマンドを使用して作成されるバインディングは何ですか?
A. ポートタイプサービスのge 0 / 2.101とポートタイプトランスポートのge 0/0の間
B. ポートタイプサービスのge 0 / 2.101とポートタイプサービスのge 0/0の間
C. ポートタイプのトランスポートのge 0 / 2.101とポートタイプのサービスのge 0/0の間
D. ポートタイプのトランスポートのge 0 / 2.101とポートタイプのトランスポートのge 0/0の間
Answer: D
Explanation: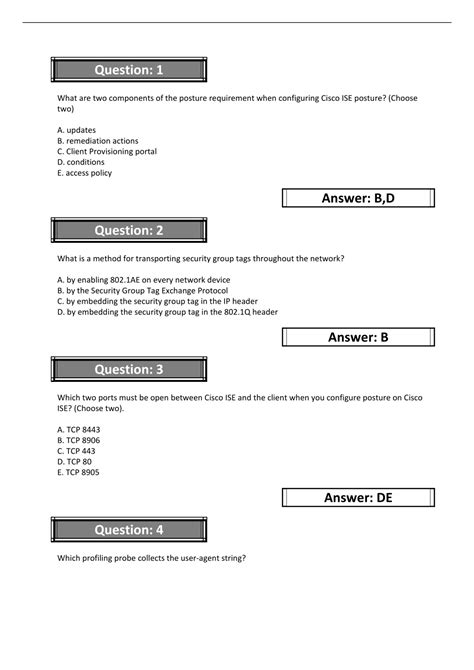
NEW QUESTION: 4
A customer has storage arrays from two different storage vendors at two different sites. The customer warts to restore operations at the secondary site in the event of a disaster.
Which VMware technology must be used to meet this requirement?
A. vSphere Fault Tolerance
B. vSphere Data Protection
C. array-based replication
D. vSphere replication
Answer: D
Soaoj is offering 100% money back guarantee on 300-715 exam prep material. If you are not satisfied with the exam results and if you are unable to pass the 300-715 exam after using our products then we can provide you 100% money back guarantee. However, if you are using our Exam dumps then you will be able to get 100% guaranteed success in the real 300-715 exam. More importantly, we offer a free 3 months updates, and you will always get latest 300-715 questions.